 Related Products
Related Products
Some results have been hidden because they may be inaccessible to you.Show inaccessible results
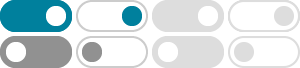
Two-step Verification | How Authentication Works
SponsoredEnable Two-Factor Authentication to Strengthen Your Security and Protect Your Data. Protect Your Accounts With Two-Factor Authentication and Prevent Unauthorized Access.Integrated Protection · Protect Your Apps · Stop Cyberattacks · Reduce Alert Fatigue 90%
Service catalog: Automated Defenses, Cloud Security, Zero Trust SecurityTop 10 Identity Access Systems | Get a Free List of Top Systems
SponsoredNo Matter Your Mission, Get The Right Identity-Access Systems To Accomplish It. Find the Best Identity Access Mgmt Systems That Will Help You Do, What You Do, Better.Trusted by Millions · Latest Industry Research · 1,000+ Categories
4/5 (1,047 reviews)

 Feedback
Feedback